You may have heard of 2-step authentication but not known exactly what it is. Let’s clear that up right now.
2-Step Verification is a way to increase the security of your account, so that no one can get into it without your permission. It uses a combination of something you know (a password) and something you have (a phone). So when you log in from a new device, the system will send you an SMS message with a code that only works for 10minutes.
You have to enter this code on your phone before you can log in!This means that even if someone finds out your password, they can’t log in unless they also have access to your phone—which is usually locked away somewhere safe.There are several benefits of using 2-step authentication, including:
- It’s easy to setup and use
- It offers an extra layer of protection against unauthorized access and account takeover
- It’s free
Unfortunately, many people are still using the old, unreliable, password only authentication. The most used password is “password” and “password123”. Birthdays, pet names, and any other public information are also easy to crack passwords.
We advise you to NOT use the same password on every account you have! It is just as leaving your car with the key in contact and the motor running in a shady neighborhood.
Even if you are not in the IT business you still need to change your passwords every two months.
How does a strong password looks like?
It is recommended to be a long string with numbers, letters and special characters. There is a usual minimum of 8 characters, but your account is much more secure with more characters.
Ex: “YKtGV]PB0y>E,+7e:>NM“
* Made using 1password.com

Why would anyone need access to your account?
- Curious hackers who want to see what kinds of things people are doing online. Sometimes they’ll do this to prove a point, or just out of curiosity. Other times they might be looking for information that could help them commit crimes against you.
- Identity thieves who want to use your email address as their own or sell it off to other criminals so they can continue committing crimes using your identity.
- People who want to use your identity in order to create scam websites or social media accounts under your name. These scammers can then use these sites to steal money or information from others by pretending they’re someone else (e.g., by impersonating an official company).
Here you may see a real life example of poor security:
“ The Darkside ransomware gang broke into Colonial Pipeline through an inactive account that didn’t use multifactor authentication, according to a consultant who investigated the attack. ” – source: https://www.crn.com/news/security/colonial-pipeline-hacked-via-inactive-account-without-mfa
Is it hard to set up 2 step authentication?
No. It is actually really easy. All you need is a smartphone.
In order to help you get started with setting up 2-step verification for your Google Account, we’ve put together this quick guide with step-by-step instructions on how to add your mobile phone number as an alternative method of signing in whenever you want to access Google services like Gmail, Calendar and Drive.
Let’s go trough the “Google mail” multi-factor authentication setup:
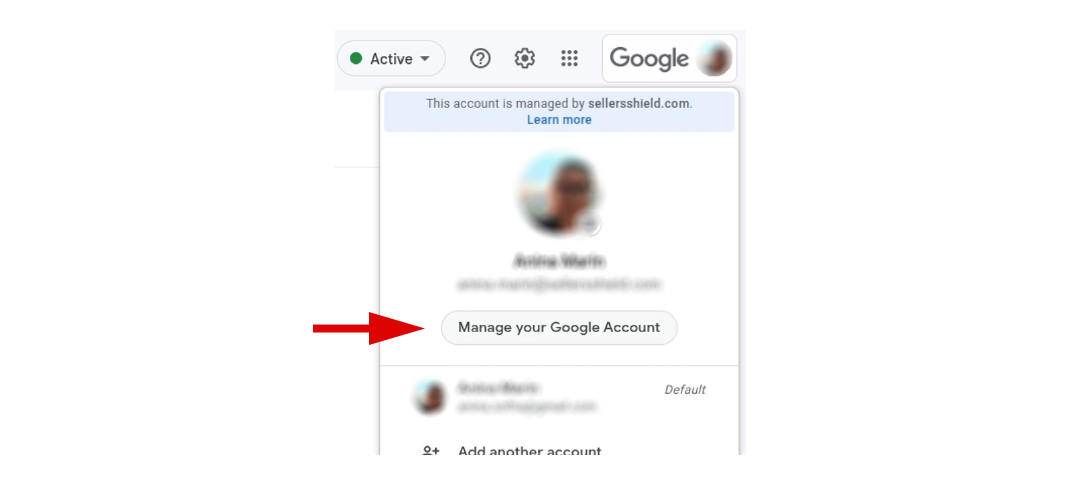
First, open your gmail and click on your profile icon (top-right usually).
Find the “Manage your google account” button.
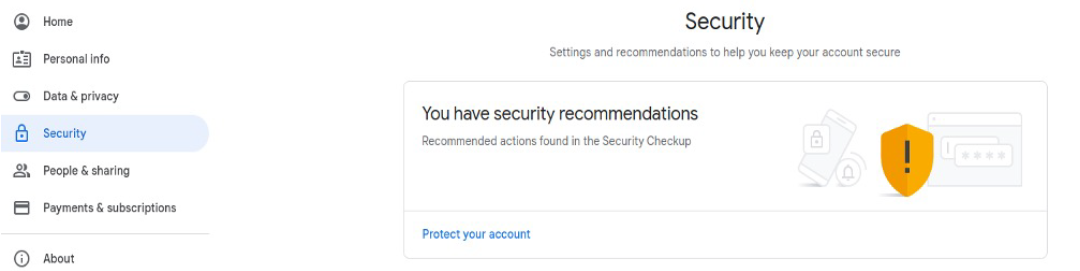
Click “Security”.
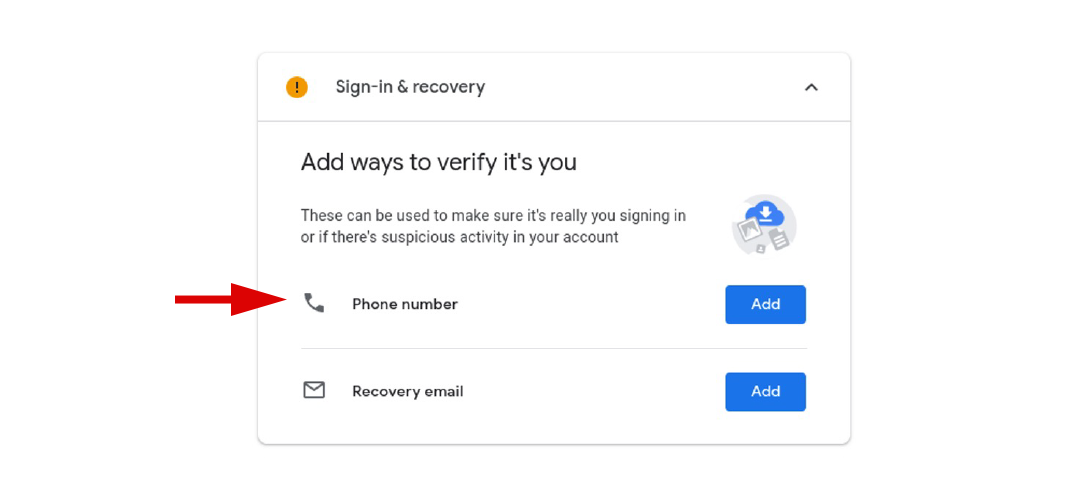
You may add your phone number and/or an alternative email:
* This is just for recovery purposes and you might need it in case you forget your password.
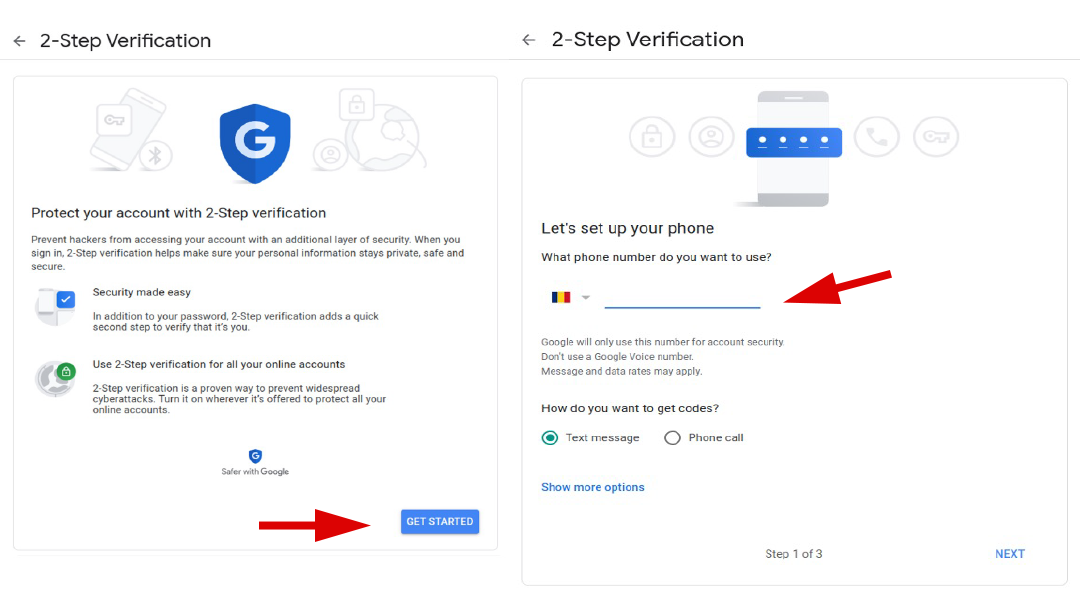
Find the section for 2 step verification. If it’s “off”, turn it on.
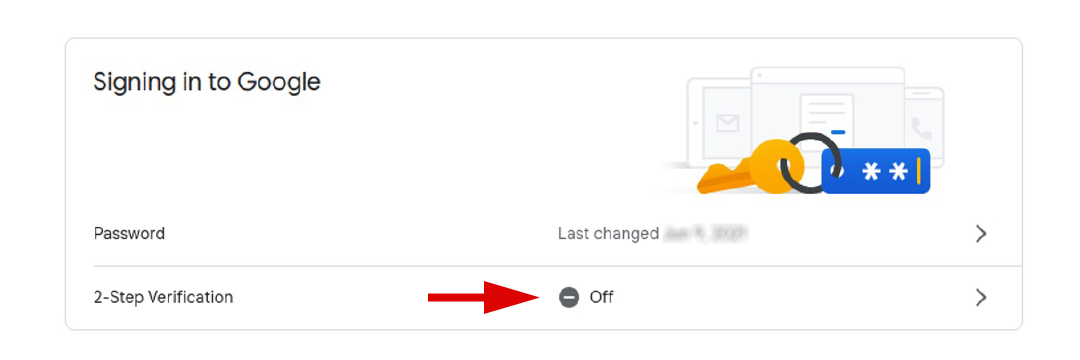
Click on the “Get started” button. Add your phone number. You will receive a message with a code. Add the code and click finish.
Find the “Authenticator app” section:
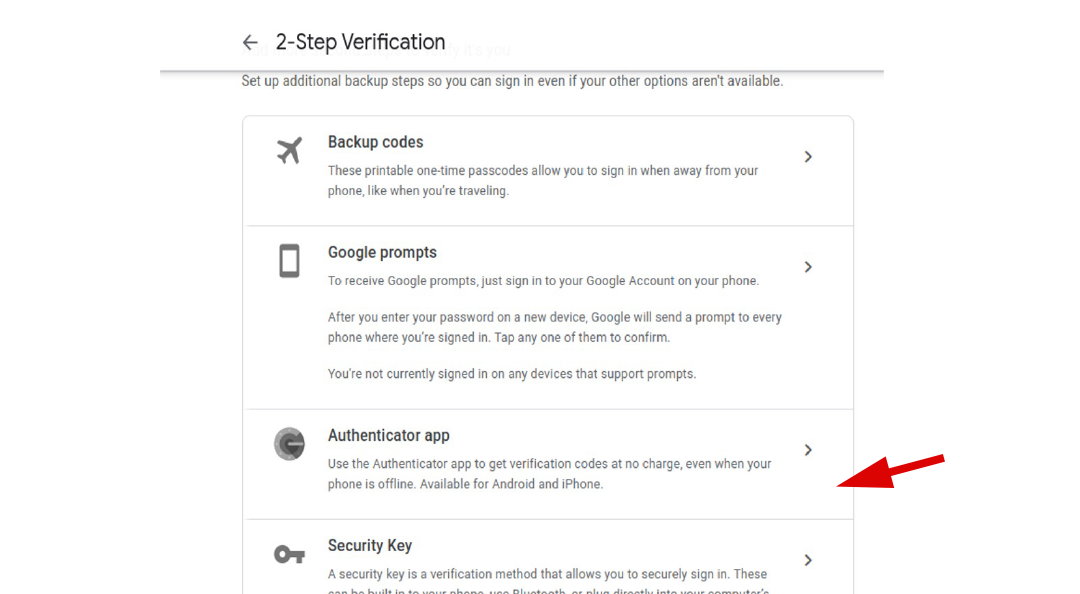
Set up the authenticator app:
You need to download and install the “Google authenticator app” from Google play (for android users). For iPhone users find and install the same application from App Store.
Open your Google Authenticator App.
Tap the “+” button.
Scan the code.
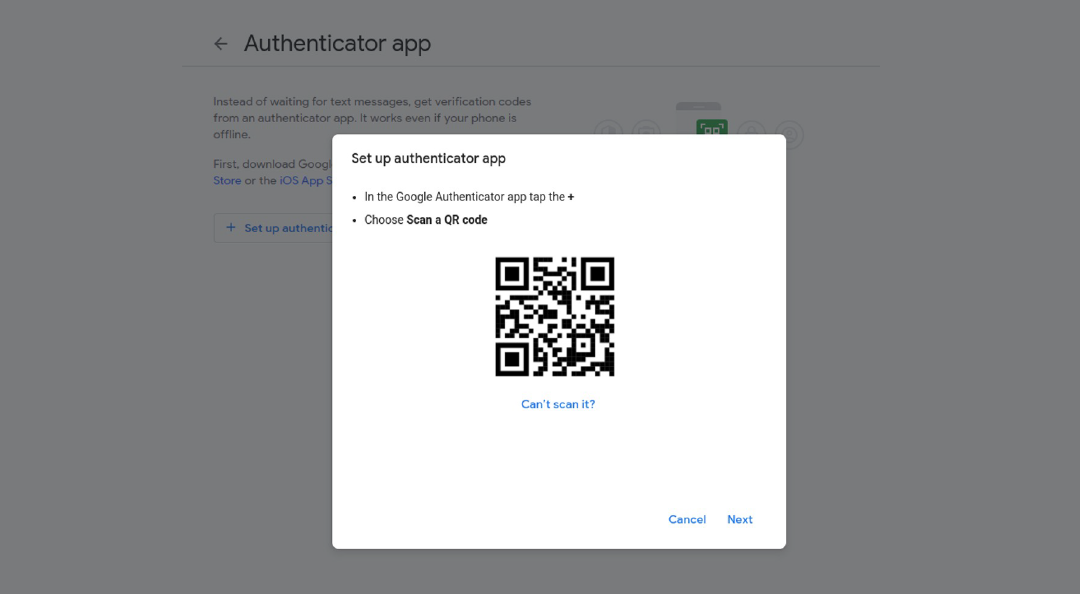
Congrats!
You are now a bit safer in the online jungle. If you want to be even more secured you may purchase a security key. Google and many others have already prepared for this type of physical protection.
You can also secure your Yahoo mail account, Facebook, GitHub and more with 2 step authentication.
Here are some links that will help you do that:
two-step verification for yahoo mail
two-factor authentication for facebook
two-factor authentication for github
Author: Anina Marin
